IT Governance Standards: COBIT, ISO17799/27001, ITIL and PMBOK – Part 2
The content of this blog is essentially material I compiled for training sessions that I ran last year. It was originally PowerPoint, but I hope that this blog version is useful. Some of the legislative stuff is probably now out of date, and it was for an Australian audience – moral of the story is to do your own research.
For part 1 of this presentation, view this post.
Framework Strengths
- COBIT is strong in IT controls and IT metrics (measurable). But it does not say how
- ISO17799 is strong in security controls but also does not say how
- ITIL is strong in IT processes (i.e. the how)
COBIT is based on established frameworks, such as the Software Engineering Institute’s Capability Maturity Model, ISO 9000, ITIL and ISO 17799. However, COBIT does not include process steps and tasks because, although it is oriented toward IT processes, it is a control and management framework rather than a process framework.
COBIT focuses on what an enterprise needs to do, not how it needs to do it. Across many aspects of an organizations activities, the board really doesn’t care about the ‘HOW’, they just want to see the ‘need’ addressed. Thus, target audience for COBIT is senior business management, senior IT management and auditors.
ITIL is based on defining best practice processes for IT service management and support, rather than on defining a broad-based control/measurement framework. It focuses on the methods and defines a more comprehensive set of processes.
Due to its high level and broad coverage and because it is based on many existing practices, COBIT is often referred to as the ‘integrator’, bringing disparate practices under one umbrella and, just as important, helping to link these various IT practices to business requirements.
ISO17799 is a more similar to COBIT than ITIL in that it is control driven, not process driven. However it is applied specifically to the area of IT security and thus drills down to a lower level than COBIT. The audience is also more focused from senior management/executive to IT and business unit management.
COBIT
- Business orientation is the main theme of COBIT
- 34 high-level control objectives
- Grouped into four domains:
- Plan and Organize
- Acquire and Implement
- Deliver and Support
- Monitor.
- IT governance guidance is also provided
- 318 Detailed control objectives (not today!)
- Maturity models, CSF, KGI, KPI
Business orientation is the main theme of COBIT. It is designed to be employed not only by users and auditors, but also, and more important, as comprehensive guidance for management and business process owners. Increasingly, business practice involves the full empowerment of business process owners so they have total responsibility for all aspects of the business process. In particular, this includes providing adequate controls. This basically means if the board is going to go down, they will take others with them!
The COBIT framework provides a tool for the business process owner that facilitates the discharge of this responsibility. The framework starts from a simple premise:
To provide the information that the organization needs to achieve its objectives, IT resources need to be managed by a set of naturally grouped processes.
From this premise, the framework continues with a set of 34 high-level control objectives, one for each "IT process". These are grouped into four domains:
- Plan and Organize
- Acquire and Implement,
- Deliver and Support
- Monitor
By addressing these 34 high-level control objectives, the business process owner can ensure that an adequate control system is provided for the IT environment.
(note my use of the term *owner* – this theme is consistent across a lot of the frameworks)
IT governance guidance is also provided in the COBIT framework. IT governance provides the structure that links
- IT processes
- IT resources
- Information
to enterprise strategies and objectives.
"IT governance integrates optimal ways of planning and organizing, acquiring and implementing, delivering and supporting, and monitoring and evaluating IT performance. IT governance enables the enterprise to take full advantage of its information, thereby maximizing benefits, capitalizing on opportunities and gaining competitive advantage."
In other words, it ensures accountability rests where it should. We will see a practical example of this in a later slide.
The governance guidelines further enhance and enable enterprise management to deal more effectively with the needs and requirements of IT governance.
The guidelines are action-oriented (activity goals) and generic, and they provide management direction for getting the enterprise’s information and related processes under control, monitoring achievement of organizational goals, monitoring performance within each IT process, and benchmarking organizational achievement.
In addition, corresponding to each of the 34 high-level control objectives is an audit guideline to enable the review of IT processes against COBIT’s 318 recommended detailed control objectives to provide management assurance and/or advice for improvement. So for example, one of the 34 high level objectives is "PO10 – Project Management." That has 14 detailed control objectives defined.
Finally, COBIT provides maturity models for control over IT processes, so management can map where the organization is today, where it stands in relation to the best in class in its industry and to international standards, and where the organization wants to be. Critical success factors (CSF’s) define the most important management-oriented implementation guidelines to achieve control over and within its IT processes. Key goal indicators (KGI’s) define measures that tell management—after the fact—whether an IT process has achieved its business requirements. Key performance indicators (KPIs) are lead indicators that define measures of how well the IT process is performing in enabling the goal to be reached.
COBIT’s enables management to answer the following types of questions:
- How far should we go and is the cost justified by the benefit?
- What are the indicators of good performance?
- What are the critical success factors?
- What are the risks of not achieving our objectives?
- What do others do?
- How do we measure and compare?
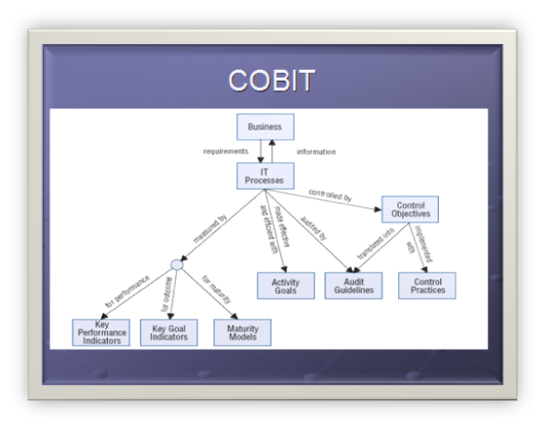
- Business requirements translate into IT Processes
- IT Processes provide information to the business
- IT Processes are controlled by control objectives
- Control objectives are implemented with control practices
- Control objectives are translated into audit guidelines
- IT processes are audited by the audit guidelines
- IT processes are made effective and efficient with activity goals
- IT processes are measured by KPI’s for performance, KGI’s for outcomes and Maturity models for maturity
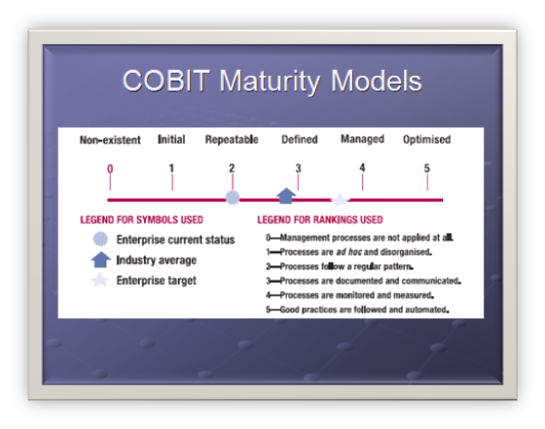
Each control objective will list the criteria that help organizations define their current ‘maturity model’ in accordance with COBiT definitions. We will see an example of this in future slides
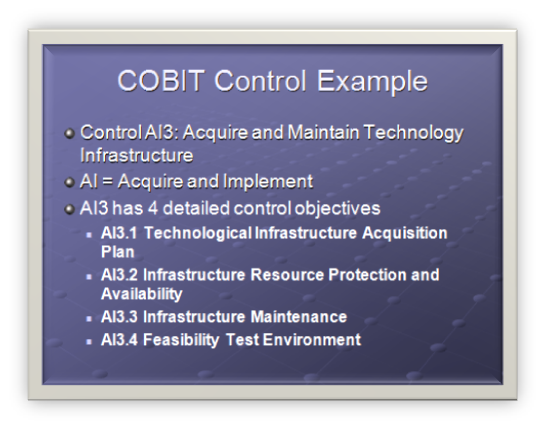
COBIT Control Example
- Control AI3: Acquire and Maintain Technology Infrastructure
- AI = Acquire and Implement
- AI3 has 4 detailed control objectives
- AI3.1 Technological Infrastructure Acquisition Plan
- AI3.2 Infrastructure Resource Protection and Availability
- AI3.3 Infrastructure Maintenance
- AI3.4 Feasibility Test Environment
High level objective: AI3
Organizations should have processes for the acquisition, implementation and upgrade of the technology infrastructure. This requires a planned approach to acquisition, maintenance and protection of infrastructure in line with agreed technology strategies and the provision of development and test environments. This ensures that there is ongoing technological support for business applications.
AI3.1 Technological Infrastructure Acquisition Plan
Produce a plan for the acquisition, implementation and maintenance of the technological infrastructure that meets established business functional and technical requirements and is in accord with the organization’s technology direction. The plan should consider future flexibility for capacity additions, transition costs, technical risks and the lifetime of the investment for technology upgrades. Assess the complexity costs and the commercial viability of the vendor and product when adding new technical capability.
AI3.2 Infrastructure Resource Protection and Availability
Implement internal control, security and auditability measures during configuration, integration and maintenance of hardware and infrastructural software to protect resources and ensure availability and integrity. Responsibilities for using sensitive infrastructure components should be clearly defined and understood by those who develop and integrate infrastructure components. Their use should be monitored and evaluated.
AI3.3 Infrastructure Maintenance
Develop a strategy and plan for infrastructure maintenance and ensure that changes are controlled in line with the organization’s change management procedure. Include periodic review against business needs, patch management and upgrade strategies, risks, vulnerabilities assessment and security requirements.
AI3.4 Feasibility Test Environment
Establish development and test environments to support effective and efficient feasibility and integration testing of applications and infrastructure in the early stages of the acquisition and development process. Consider functionality, hardware and software configuration, integration and performance testing, migration between environments, version control, test data and tools, and security.
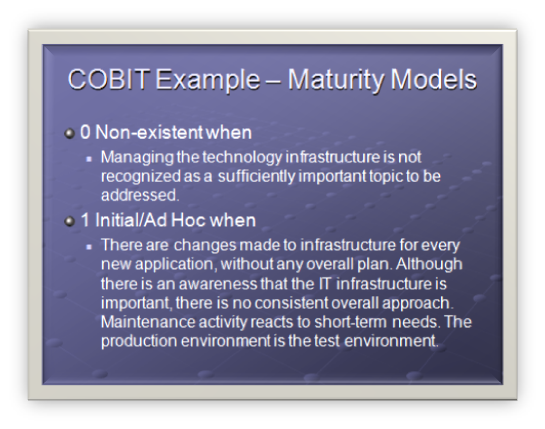
I have only listed 2 of the maturity models here but it gives you an idea of what is required even at the basic levels. Where does your employer fit here? 🙂
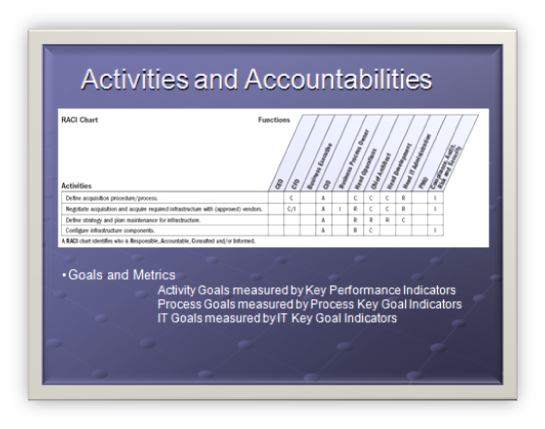
This where the accountability comes in.
- R: Responsible
- A: Accountable
- C: Consulted
- I: Informed
Accountability defines what activity goals exist for a high control and who has what accountability. For example:
"Define strategy and plan maintenance for infrastructure" understandably does not involve the CEO or CFO. The CIO is accountable – or the owner of this activity. Responsibility (custodianship) is shared between the roles of:
- Head Operations
- Chief Architect
- Head of Development
Compliance, Audit, Risk and Security personnel are to be informed of the activity goals.
In the next part of this series, we will examine ITIL and then ISO17799
For the next post of this topic, consult this post.



